Create Product Catalog Application
This workshop has been deprecated and archived. The new Amazon EKS Workshop is now available at www.eksworkshop.com.
Let’s create the Product Catalog Application!
Build Application Services
Build and Push the Container images to ECR for all the three services
cd eks-app-mesh-polyglot-demo
aws ecr get-login-password --region $AWS_REGION | docker login --username AWS --password-stdin $ACCOUNT_ID.dkr.ecr.$AWS_REGION.amazonaws.com
PROJECT_NAME=eks-app-mesh-demo
export APP_VERSION=1.0
for app in catalog_detail product_catalog frontend_node; do
aws ecr describe-repositories --repository-name $PROJECT_NAME/$app >/dev/null 2>&1 || \
aws ecr create-repository --repository-name $PROJECT_NAME/$app >/dev/null
TARGET=$ACCOUNT_ID.dkr.ecr.$AWS_REGION.amazonaws.com/$PROJECT_NAME/$app:$APP_VERSION
docker build -t $TARGET apps/$app
docker push $TARGET
done
Building/Pushing Container images first time to ECR may take around 3-5 minutes
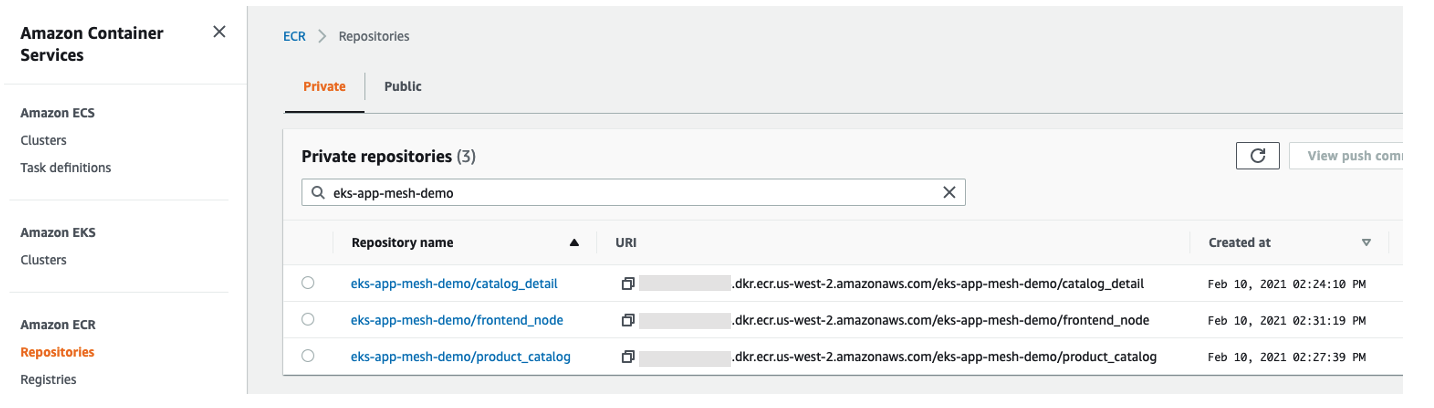
Once completed, you can confirm the images are in ECR by logging into the console
Deploy the Application Services to EKS
envsubst < ./deployment/base_app.yaml | kubectl apply -f -
Fargate pod creation for prodcatalog service may take 3 to 4 minutes
Get the deployment details
kubectl get deployment,pods,svc -n prodcatalog-ns -o wide
You can see that:
-
Product Catalog service was deployed to
Fargatepod as it matched the configuration (namespaceprodcatalog-nsand pod spec label asapp= prodcatalog) that we had specified when creating fargate profile -
And other services Frontend and Catalog Product Detail were deployed into
Managed Nodegroup
Confirm that the fargate pod is using the Service Account role
export BE_POD_NAME=$(kubectl get pods -n prodcatalog-ns -l app=prodcatalog -o jsonpath='{.items[].metadata.name}')
kubectl describe pod ${BE_POD_NAME} -n prodcatalog-ns | grep 'AWS_ROLE_ARN\|AWS_WEB_IDENTITY_TOKEN_FILE\|serviceaccount'
You should see the below output which has the same role that we had associated with the Service Account as part of Fargate setup.
Confirm that the fargate pod logging is enabled
kubectl describe pod ${BE_POD_NAME} -n prodcatalog-ns | grep LoggingEnabled
We can see the confirmation in the events that says Successfully enabled logging for pod.