Amazon EKS Workshop > Beginner > Encrypting Secrets with AWS Key Management Service (KMS) Keys > Access the Secret from a Pod
Access the Secret from a Pod
This workshop has been deprecated and archived. The new Amazon EKS Workshop is now available at www.eksworkshop.com.
Deploy a Pod to Consume the Secret
Create a YAML file (podconsumingsecret.yaml) with the following pod definition:
cat << EOF > podconsumingsecret.yaml
---
apiVersion: v1
kind: Pod
metadata:
name: consumesecret
spec:
containers:
- name: shell
image: amazonlinux:2
command:
- "bin/bash"
- "-c"
- "cat /tmp/test-creds && sleep 10000"
volumeMounts:
- name: sec
mountPath: "/tmp"
readOnly: true
volumes:
- name: sec
secret:
secretName: test-creds
EOF
Deploy the pod on your EKS cluster:
kubectl --namespace secretslab \
apply -f podconsumingsecret.yaml
Output:
Attach to the pod and attempt to access the secret:
kubectl --namespace secretslab exec -it consumesecret -- cat /tmp/test-creds
Output:
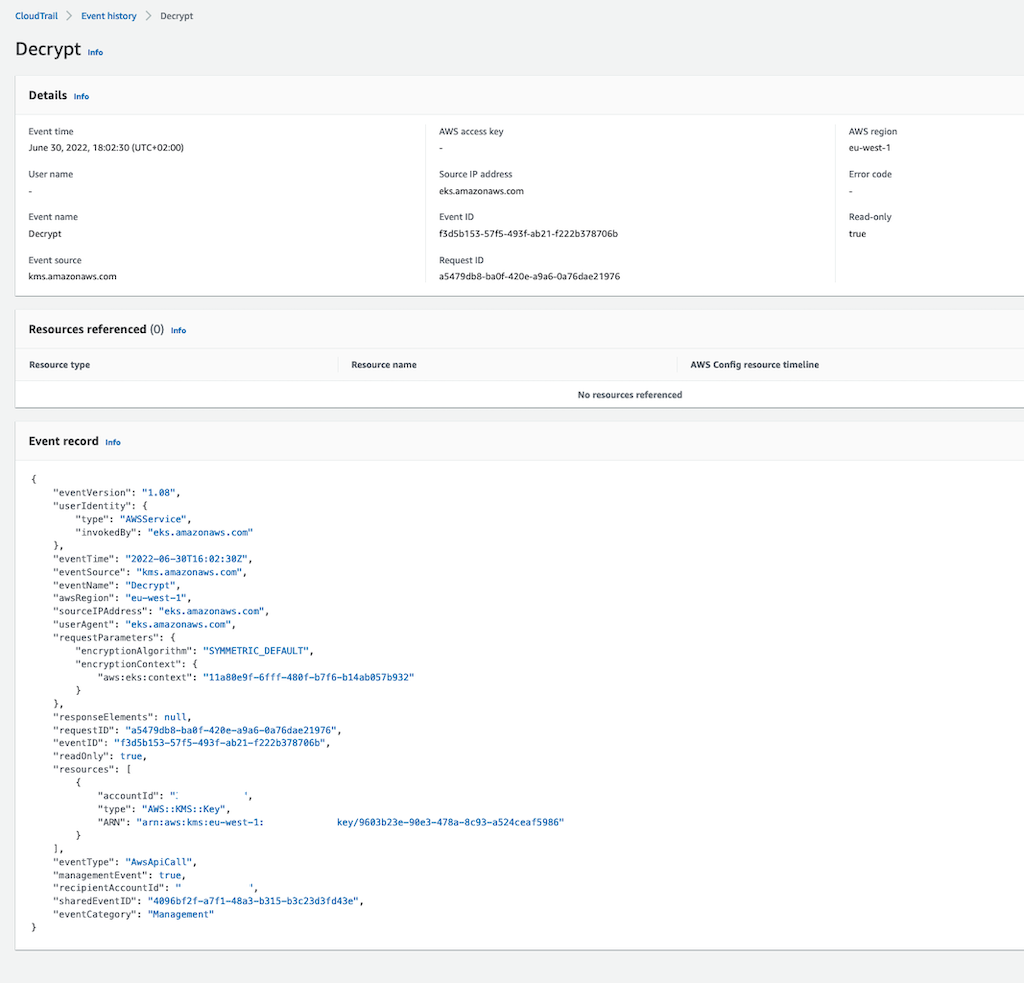
Let’s see if the CloudTrail event for our secret retrieval is now visible. If you go to CloudTrail you should see a record available if you search for the Event name Decrypt with output similar to the following screenshot. If the event hasn’t shown up yet, wait a few minutes and try again.
On the next screen, you will perform the cleanup operations for this lab.